KNIME Secrets
Role
UX/UI Designer I Project Manager
Tools
KNIME is a powerful data analytics software that enables users to process and manipulate data through a node-based workflow system. It consists of two key components:
✔ KNIME Analytics Platform – where users create and execute workflows.
✔ KNIME Hub – an online portal for sharing, managing, and publishing workflows.
Users build workflows by connecting nodes to define data inputs, transformations, and outputs (e.g., charts, reports). However, as workflows are often shared among teams or published online, data security became a critical concern. Without proper safeguards, sensitive information could be accidentally exposed or manipulated with fraudulent intent.
To address this, we developed KNIME Secrets—a multi-level security system designed to protect sensitive workflows from unauthorized access and unintended data leaks.
This system provides:
🔐 Granular security controls at the User, Team, and Global levels.
⚡ Seamless integration with existing KNIME workflows without disrupting usability.
✅ A centralized safety mechanism that ensures confidential data remains protected while maintaining workflow flexibility.
As the UX/UI Designer, I was responsible for creating an intuitive authentication system that translates complex security infrastructure into a user-friendly experience. Beyond design, I also played a key coordination role between frontend and backend teams, ensuring smooth execution by aligning technical constraints with UX goals. Additionally, I introduced a structured Figma documentation system to enhance collaboration and streamline future iterations of the project.
This project challenged me to balance usability, security, and technical feasibility, ensuring that KNIME Secrets not only protects user data but also integrates effortlessly into their existing workflows.
OVERVIEW & CONTEXT
PROCESS & METODOLOGY
1.
Research & User Insights
To ground my design decisions in real user needs, I:
✔ Observed user interactions to identify pain points and usability challenges.
✔ Engaged with users through the KNIME forum, gathering direct feedback on their security concerns.
✔ Consulted stakeholders to align on business and technical requirements.
✔ Analyzed industry standards, studying best practices in data protection and authentication systems to create a solution that balances security with ease of use.
2.
Wireframing & Prototyping
With a solid research foundation, I:
✔ Sketched initial wireframes, ensuring that the authentication flow was both secure and intuitive.
✔ Iterated based on testing and feedback, refining usability while keeping backend constraints in mind.
✔ Developed high-fidelity designs, optimizing accessibility and learnability.
3.
Implementation & Collaboration
To ensure seamless execution, I:
✔ Coordinated the teams, aligning development efforts with design goals.
✔ Worked closely with backend engineers, translating technical requirements into user-friendly experiences.
✔ Established a structured Figma system, organizing design files and documentation for clarity and scalability.
PROTOTYPING
- Interactive prototypes with Figma to validate design concepts and workflows.
- Usability testing with potential users and refined the Secrets structure based on feedback. Testing was done internally with new users, mid-knowledge users and power users, in order to understand if the level of complexity was easy to learn and to test that all user needs were met.
DESIGNS & PROCESS
Consistency
Within KNIME Hub – KNIME´s online tool where the Secrets are created, managed and stored – we established as part of our structure to keep each page with a frame including the main and secondary navigation, a main body with the main contents of the page and the use of side panels for all actions of creation and management. Therefore,
I´ve kept this structure when designing Secrets, keeping the flow consistent for the users.
Structure
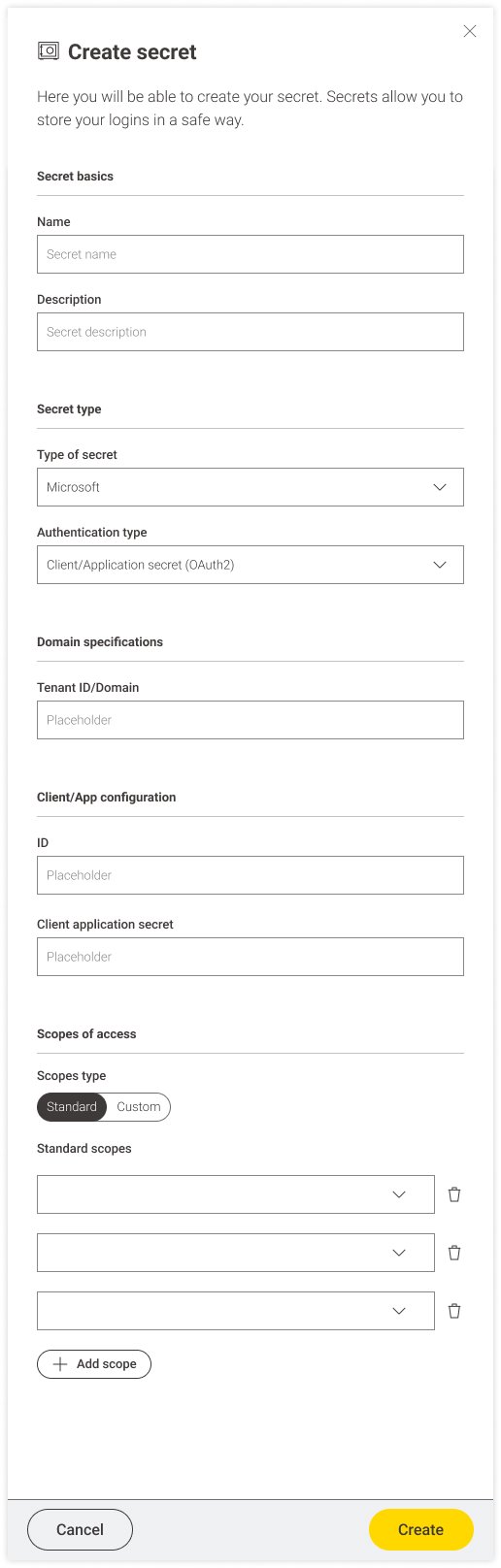
The structure of the Secrets is meant to help and guide the user within the creation - and later editing - of the many components of the secret itself.
Therefore I developed a structure that starts with basic elements that are common for all Secrets, but then builds us with the type- specific components.
HERE YOU CAN SEE THREE DIFFERENT TYPES OF SECRETS
Secret basics help the user to identify the Secret and add a description, ensuring there is no confusion between Secrets in the future
The selection of the Secret type is where the construction of the Secret starts: this selection will determine the following fields that are strictly type specific.
There are 9 different types of Secrets – each with up to 3 internal variants.
Secret pages on KNIME Hub
On KNIME Hub is where the Secrets can be created, edited, stored and are visualised in their specific page.
The Secrets page allows for a quick overview of not only whet are the secrets each user has created, but also of all the Secrets shared with them, what secrets are active, which ones require to log in and which ones have been made inactive.
Users when creating a Secret have the possibility to share them directly with other users, and edit permissions through time. When a Secret is shared with a user – for example within a Team – the user will be able to use the Secret and see it, but won’t be able to modify it since that’s only possible for the Secret creator and Admins.
IMPLEMENTATION, LAUNCH & EVALUATION
Collaborated closely & lead frontend and backend teams to ensure seamless and accurate implementation of the design.
Provided comprehensive design assets and documentation, streamlining the development process and ensuring clarity.
Led presentations and knowledge-sharing sessions, empowering teams to work independently while maintaining design consistency.
Collected internal feedback from users at different levels, refining the system based on real-world usage insights.
Documented user feedback from the KNIME Forum, identifying areas for improvement and future iterations.
Facilitated large-scale distribution of the security system, ensuring successful adoption across both B2B and B2C clients.
Deep Dive into the Process
Working on KNIME Secrets meant being deeply involved from the very beginning. This included actively participating in backend and architecture discussions—not from a technical standpoint, but from a product perspective. These conversations were essential for gaining a clear understanding of technical constraints and future implementation possibilities.
This collaboration was a two-way exchange:
✔ It enabled me to design assets that were fully aligned with technical requirements from the outset.
✔ It helped the backend team better understand design constraints, fostering a more user-centered approach to development.
By bridging the gap between technical feasibility and user experience, I ensured that KNIME Secrets was not only secure and robust but also intuitive and accessible.
Structure & Clarity
As the sole designer responsible for implementing KNIME Secrets, I took the initiative to establish a clear and organized system for our Figma files. I structured them into distinct sections, each dedicated to a specific aspect of the project—Secrets pages, Secret types, archive, and more.
This approach ensured:
✔ Clarity in presentations for product owners and developers.
✔ A seamless handover, enabling developers to work independently with minimal friction.
✔ A well-documented, scalable system, maintaining consistency between designs, discussions, and documentation from day one.
By prioritizing structure and accessibility, I helped create a streamlined workflow that enhanced collaboration and efficiency across teams.
CONCLUSION
🚀 Created a complex security system with user-friendly interface and user experience.
🔐 Increased adoption rates by making data protection more accessible and intuitive.
✅ Streamlined collaboration between design and development, improving efficiency for future updates.
By combining user research, iterative design, and cross-team collaboration, I helped KNIME Secrets evolve into a powerful yet approachable security feature, ensuring that users can protect their workflows with confidence.